As lockdown continues and uncertainty grows around how and when we can return to normal, governments and companies believe they have found the solution in technology. Contact tracing apps are being hailed as the best solution both to tracking people diagnosed with Covid-19 and alerting others who may have been infected so they can self quarantine, allowing healthy people to move around freely and return to work.
Governments around the globe have been rolling out these apps to varying degrees of success and compliance. From China to Iceland, citizens are being asked to download an app to their smartphone and input personal details and information about their health. The UK government recently released its app, built in collaboration with the NHS, and France is also launching a testing phase of its app, StopCovid, in the coming weeks.
The idea behind these apps is to make contact tracing easier and faster. Mapping the spread of the infection currently involves manually tracking the number of people who could have come into contact with an infected person, so will an app make that easier?
How the apps work
In theory, yes. Downloading and registering with these apps will allow users to be informed if they have been close to someone diagnosed with Covid-19 or to inform others that they are infected with the disease.
The app is able to do this because it is monitoring the users’ location and the location of other app users nearby. European governments are mostly using apps with Bluetooth technology as a way to track and inform people about their risk of contracting Covid-19. On a smartphone, Bluetooth works by exchanging an anonymous signal with other smartphone users – like a kind of virtual handshake. This exchange will either be recorded anonymously on the app, or stored in a central database, during which time, if a user tests positive for Covid-19 they can update the app with their health information, and an alert is sent out to those who have been in near contact with them. But it is not as simple as it sounds.
It’s all about reliability
For the app to work effectively a large number of users must sign up to use it. A small number of users means that it will be difficult to carry out the extensive contact tracing that is needed to contain the disease. This means governments are going to have to convince citizens that these apps are worth downloading and using.
The fact that everyone needs to have a smartphone in order to use the app is another barrier. Not everyone can afford a smartphone or is able to use one. This risks isolating the elderly, the homeless, people living in poverty, and asylum seekers and refugees. Groups that are at high risk of catching Covid-19 due to their age or inability to self isolate.
Experts are also concerned about the reliability of the app as a way of gathering data. The app will not be able to tell users whether the person who was infected was wearing a mask, or whether they were standing behind a window or door. This is likely to lead to people being told to self quarantine when they do not need to. Too many false alerts and they could abandon using the app. People who have Covid-19 may leave the house without their phone or leave it in their vehicle meaning that people who have come into contact with them would not be alerted to the risk of infection.
What about privacy?
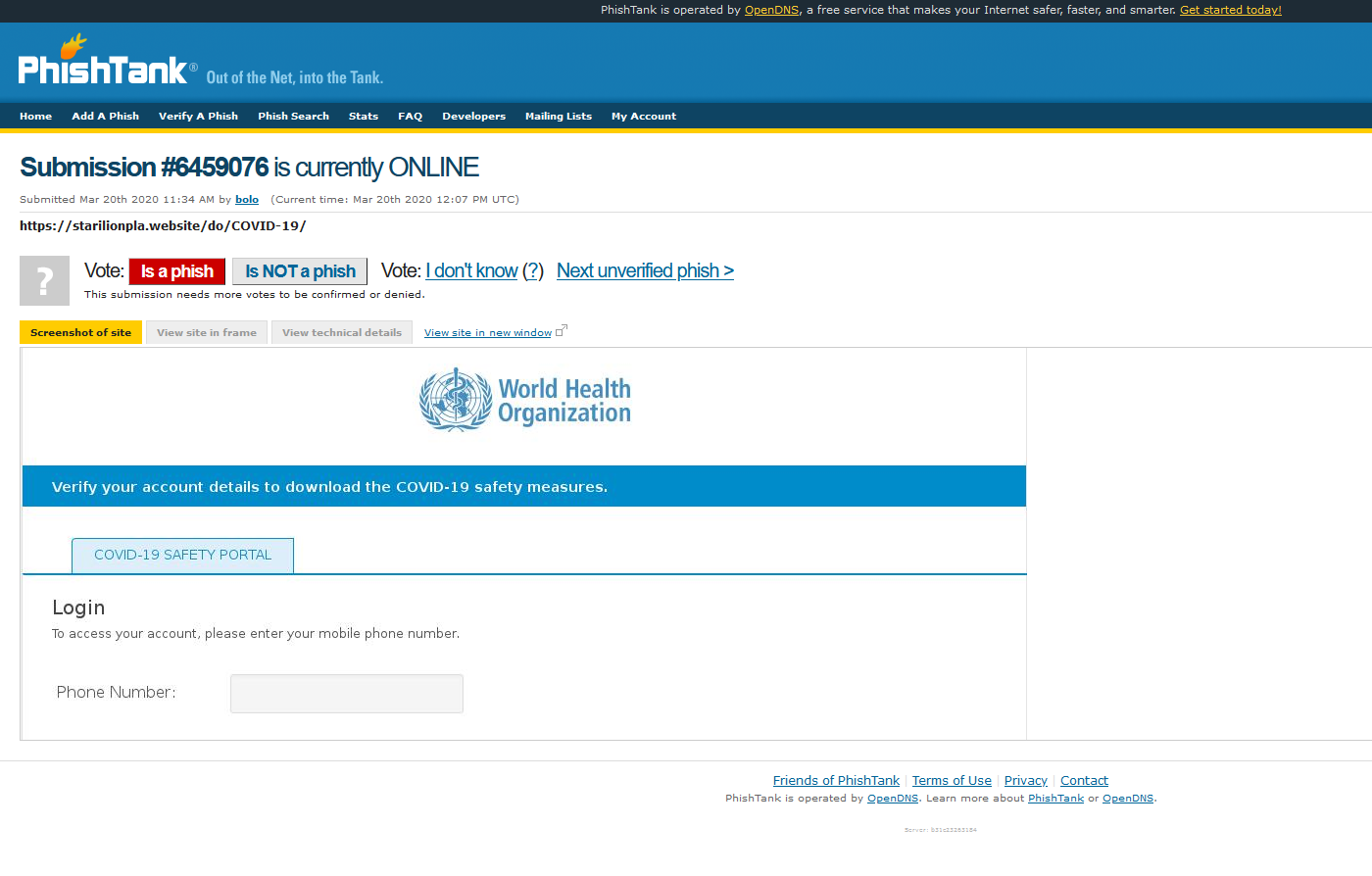
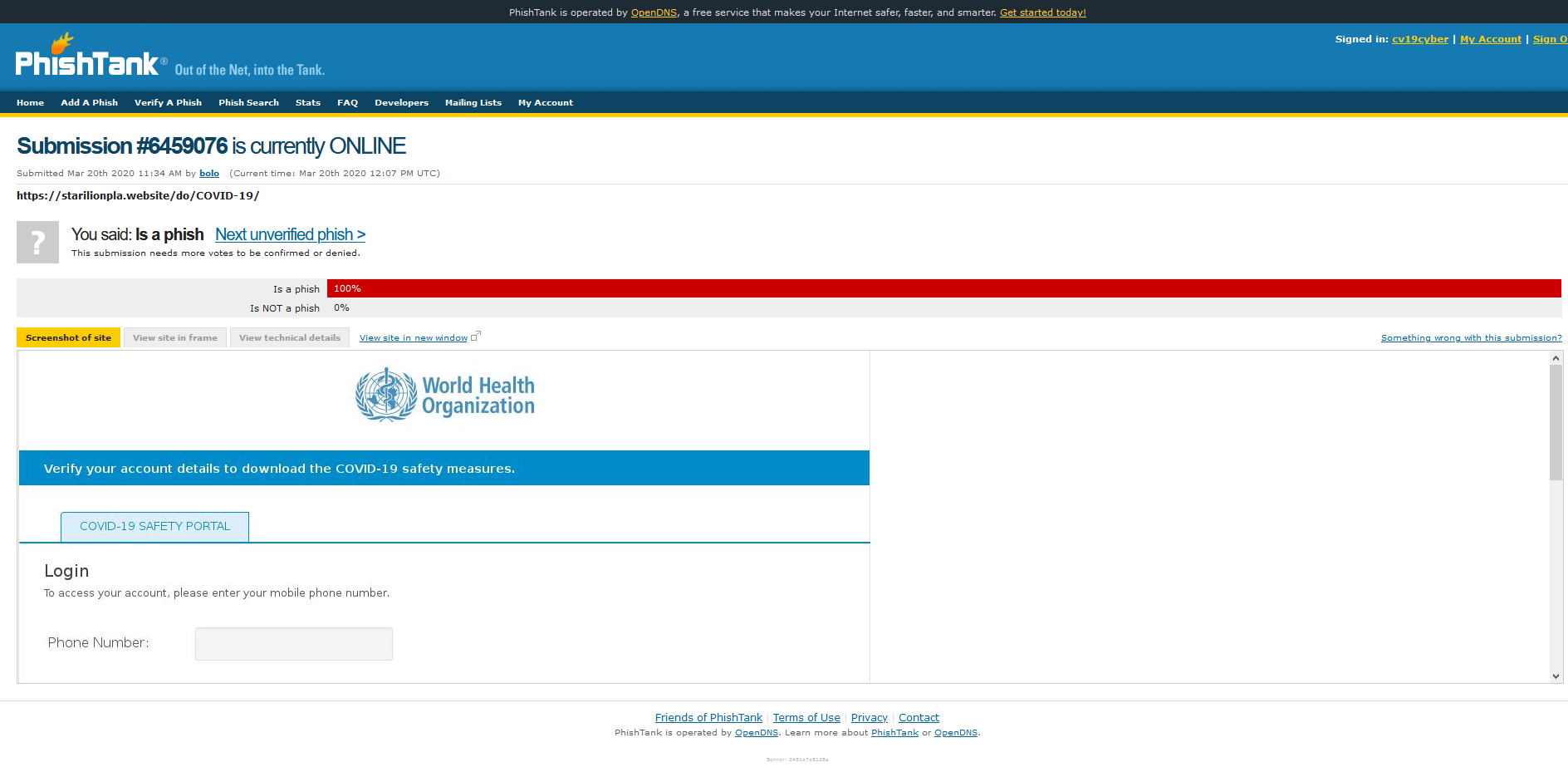
And there is also the issue of privacy. Experts are increasingly concerned about the amount of data these apps collect, where this data is stored, and who has access to it. Data, even anonymous data, relating to people’s health can be a valuable asset for businesses and governments alike. What information is collected and who can see this information will vary depending on government policy and practice as well as how the app is designed and built.
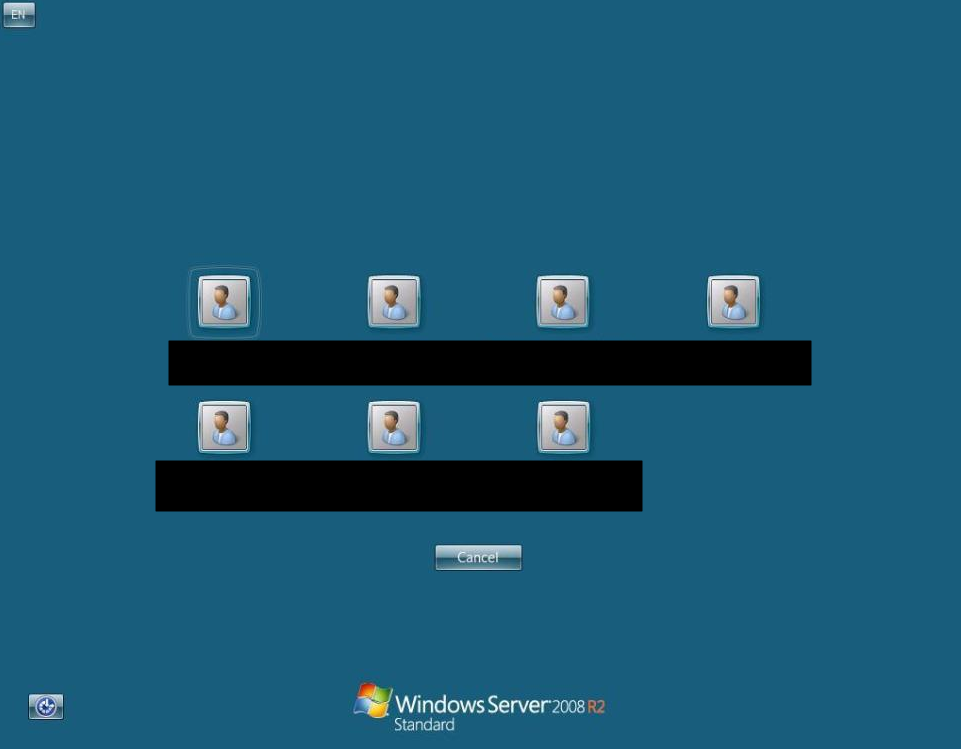
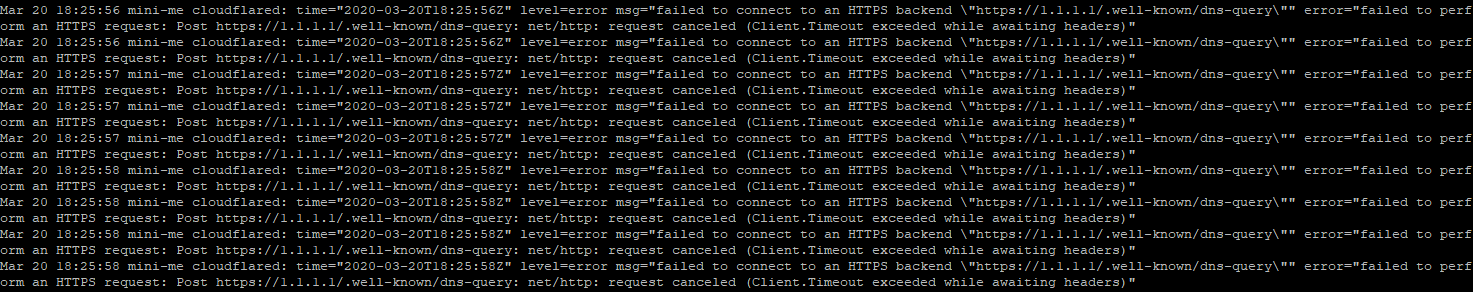
Apps can either use a centralised database or a decentralised one. A centralised database, like the one the NHS app will use, means that data is stored on a central server and that the information can be accessed by others, both officially, by government, and unofficially, by criminals. While a centralised database allows governments and companies access to a greater data pool, which would allow them to better understand the spread of Covid-19, this database, like all databases, is vulnerable to abuse.
Apple and Google recently announced a partnership that would allow for a decentralised server. This would mean that anonymised contact tracing would be carried out by individual phones and not from a central server. This approach is currently being adopted by a number of governments around the world. The lack of a central server means that the authorities will not have access to user data which means that while there is less opportunity to investigate Covid-19, user information is more secure.
Whichever method is being used to collect data, privacy experts are keen to stress that checks and balances are necessary to ensure that apps are not being used to surveil and track users long after Covid-19 is past. And none of these apps are the magic solution – we need testing, social distancing, and ultimately, a vaccine before we start to turn the tide on Covid-19.
This guest blog was kindly written by Ela Stapley