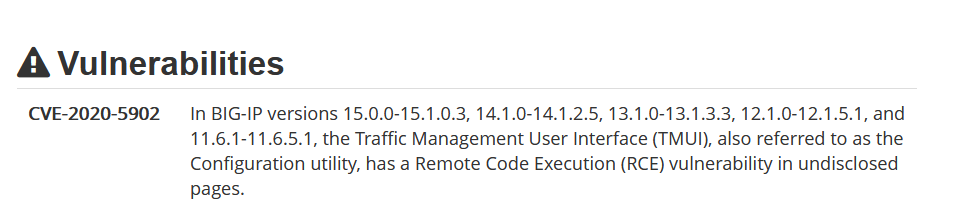
F5 Traffic Management User Interface (TMUI) Remote Code Execution (CVE-2020-5902) & XSS (CVE-2020-5903)
https://support.f5.com/csp/article/K52145254
https://support.f5.com/csp/article/K43638305
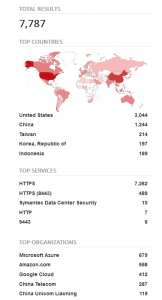
A critical vulnerability exists (CVE-2020-5902) that can lead to remove code execution from an unauthenticated network perspective. The vulnerability exists in the management interface, by good practise these interfaces would be on a private restricted network however we know this is not always the case as we can see from Shodan:
https://www.shodan.io/search?query=http.favicon.hash%3A-335242539
This vulnerability has an active POC exploit in the wild covering path traversal to file read through to remote code execution. Examples of both the Metasploit module and public intel on HTTP requests are here:
https://github.com/rapid7/metasploit-framework/pull/13807
https://github.com/jas502n/CVE-2020-5902/
We strongly recommend management interfaces are not exposed to the internet, consider:
- Removing the interface from the internet
- Using IP Whitelisting to restrict traffic flows
- Using a VPN and/or jump box solution to perform sensitive remote administration tasks
- Restrict access using a management traffic interface/route
- Patch the vulnerable devices
Palo Alto Networks PA-OS Authentication Bypass (CVE-2020-2021)
https://security.paloaltonetworks.com/CVE-2020-2021
When Security Assertion Mark-up Language (SAML) authentication is enabled and the ‘Validate Identity Provider Certificate’ option is disabled (unchecked), improper verification of signatures in PAN-OS SAML authentication enables an unauthenticated network-based attacker to access protected resources. The attacker must have network access to the vulnerable server to exploit this vulnerability.
This vulnerability requires specific conditions to exist (which are not good practise from a Palo Alto deployment best practise point of view) so whilst this is still critical, it is wise to conduct a configuration review and take appropriate action.
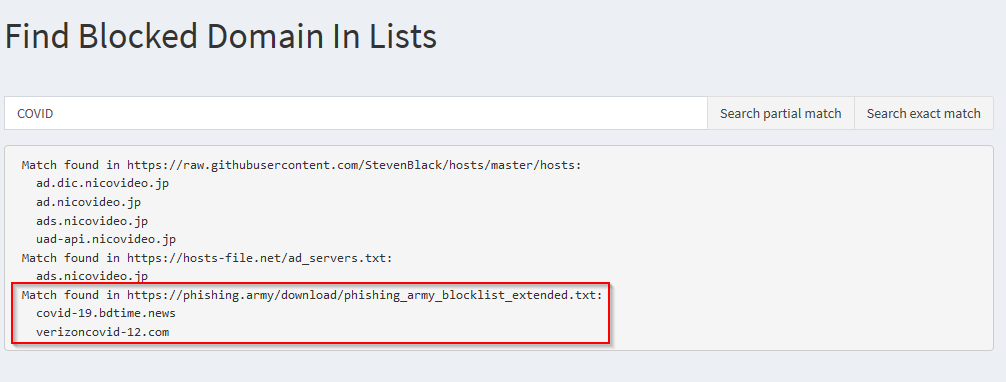
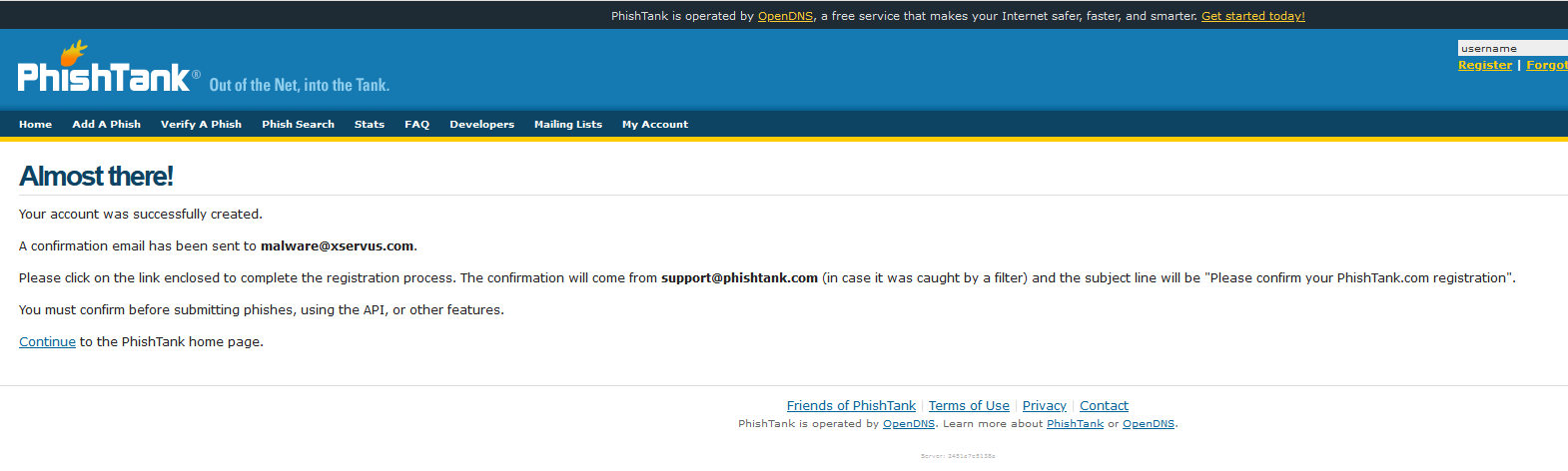
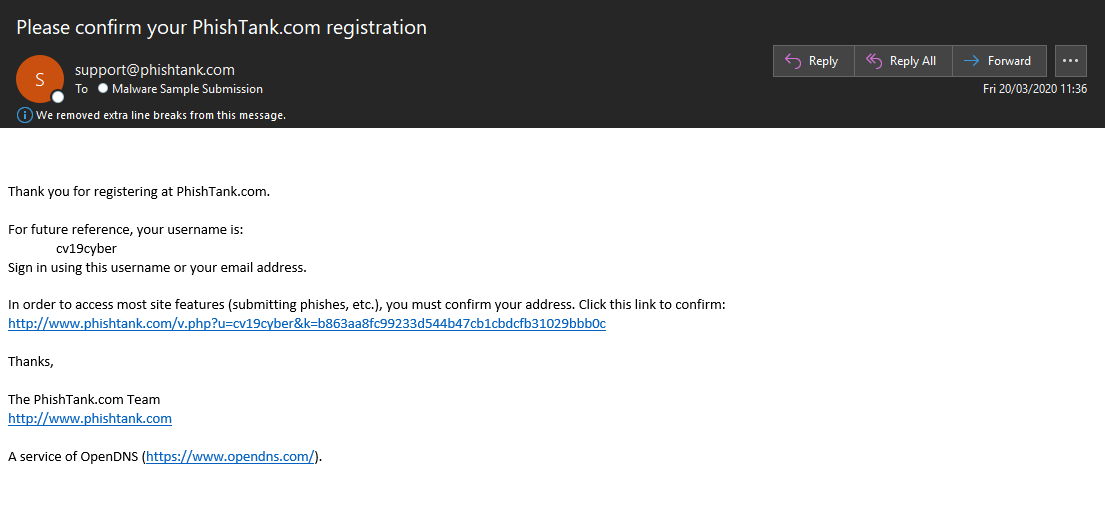
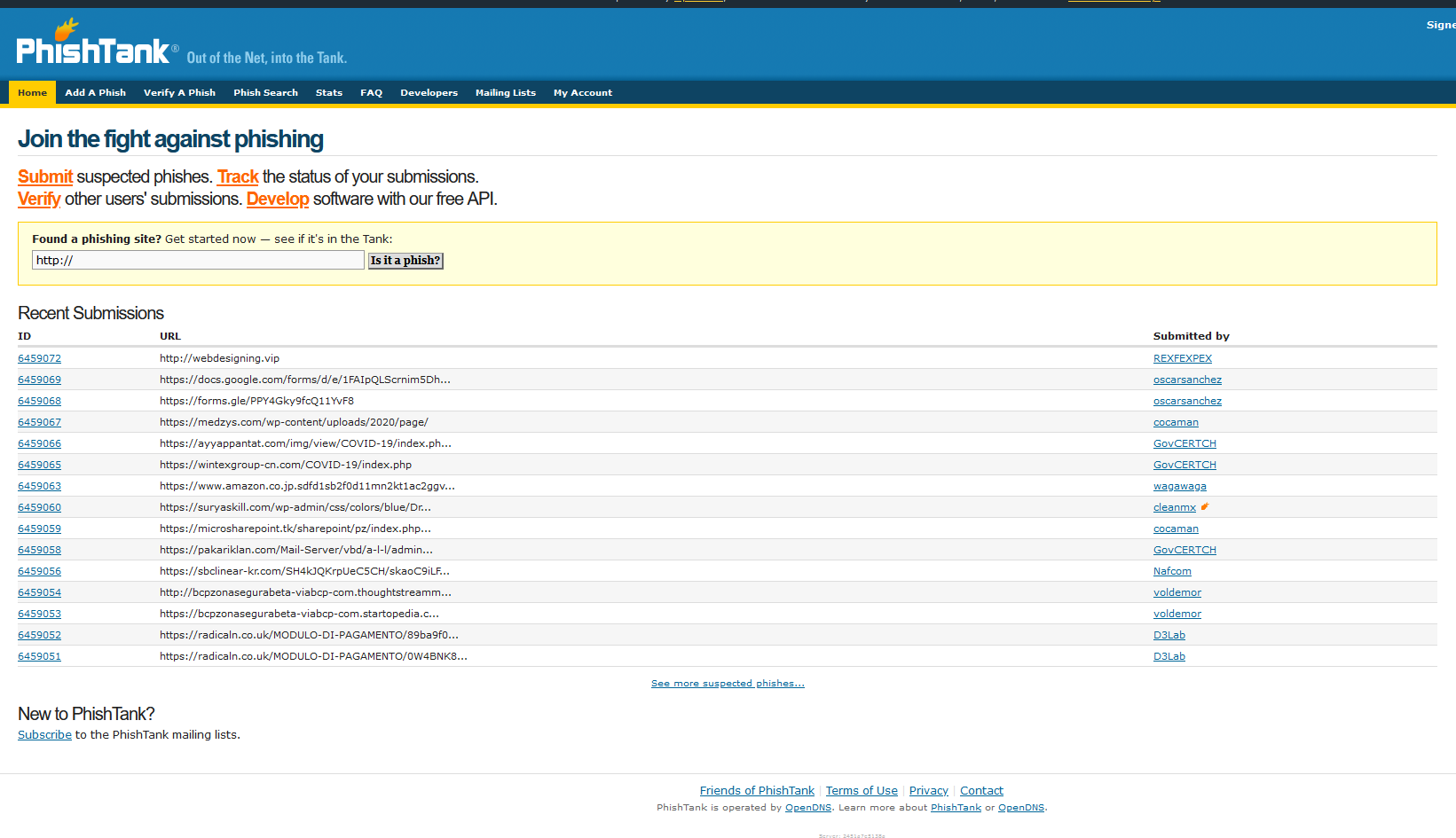
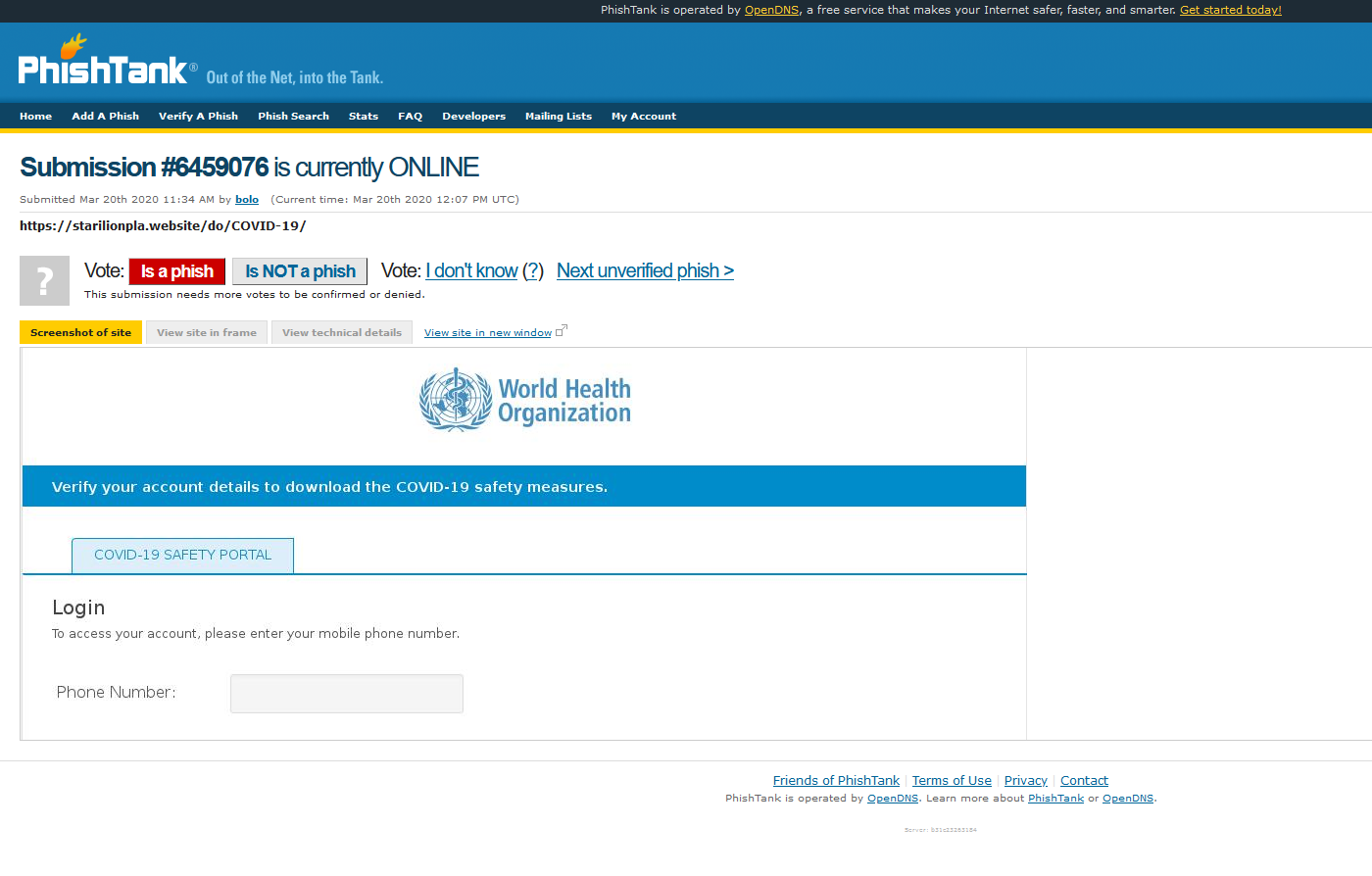
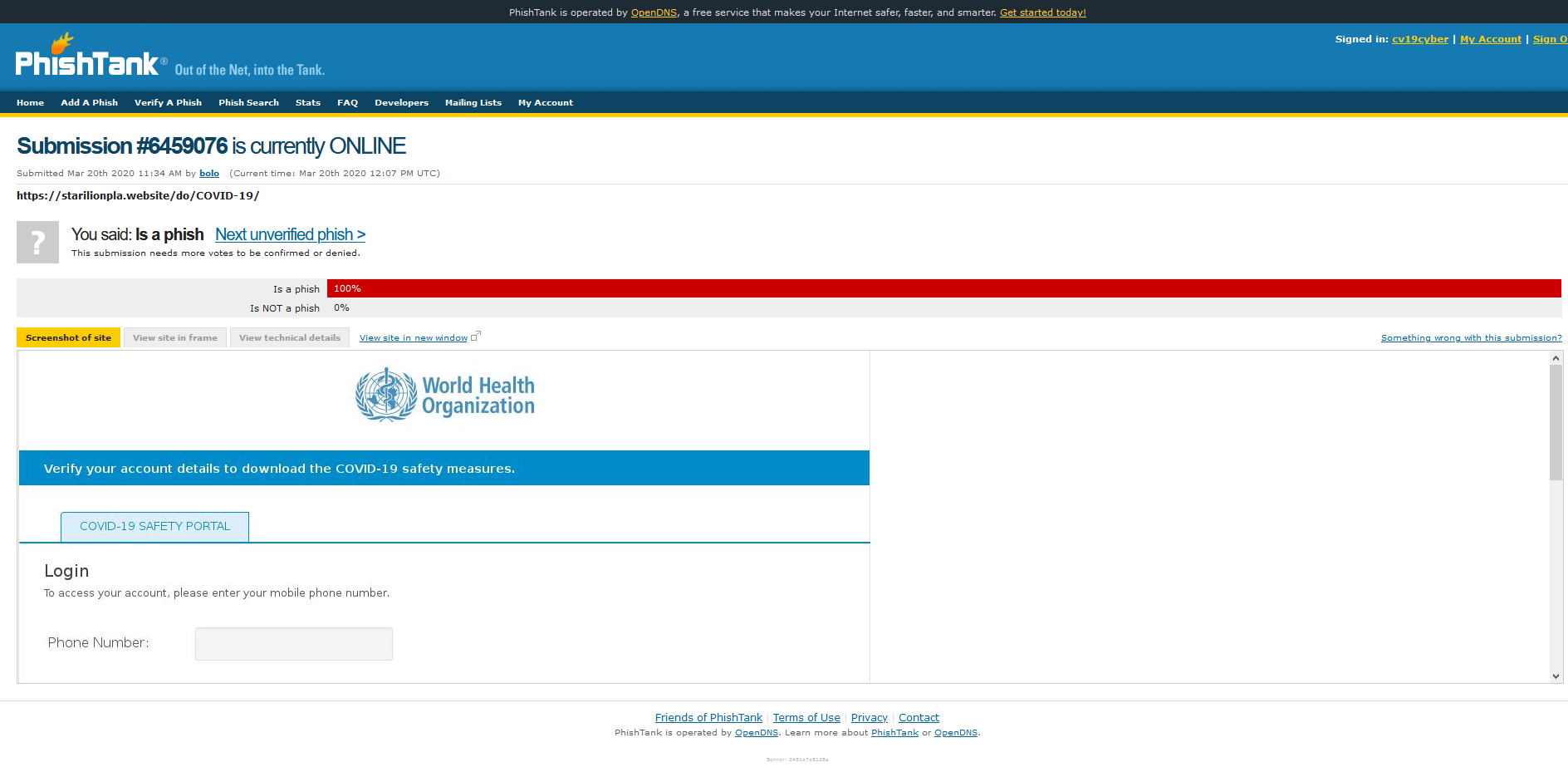
Phishing
Phishing is a constant threat scenario, during the COVID pandemic we have seen lures adapted to take advantage of a range of situations, as always leveraging FUD and high-pressure scenarios such as PPE, Corona Virus testing equipment etc.
From an internet facing perspective we see the following generalisations:
- Poor coverage of SPF, DMARC and DKIM deployment
- Misconfiguration of mail protection records
Whilst we advocate security awareness with staff members, during a time of increased pressure it is just as (potentially more so) to leverage technical controls as well as soft controls to help combat the likelihood of a phishing incident achieving impact.
Useful Resources
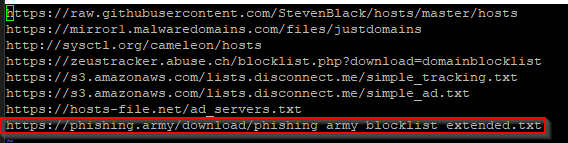
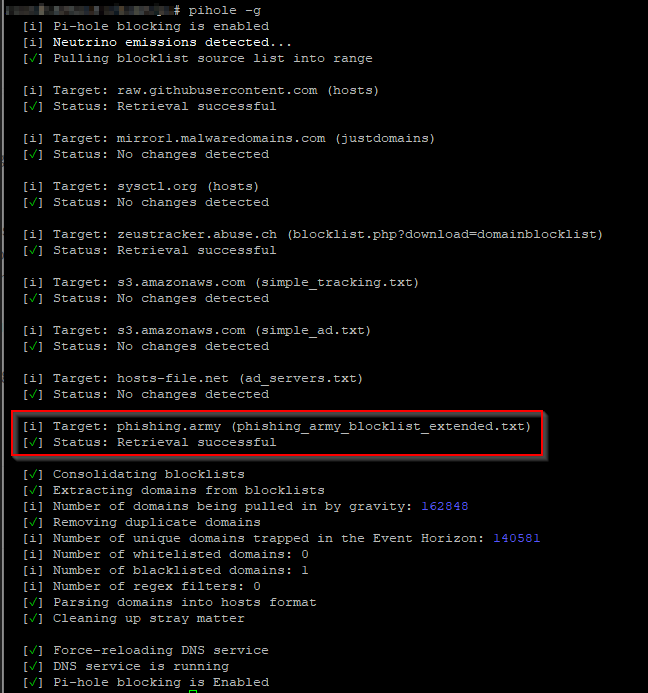
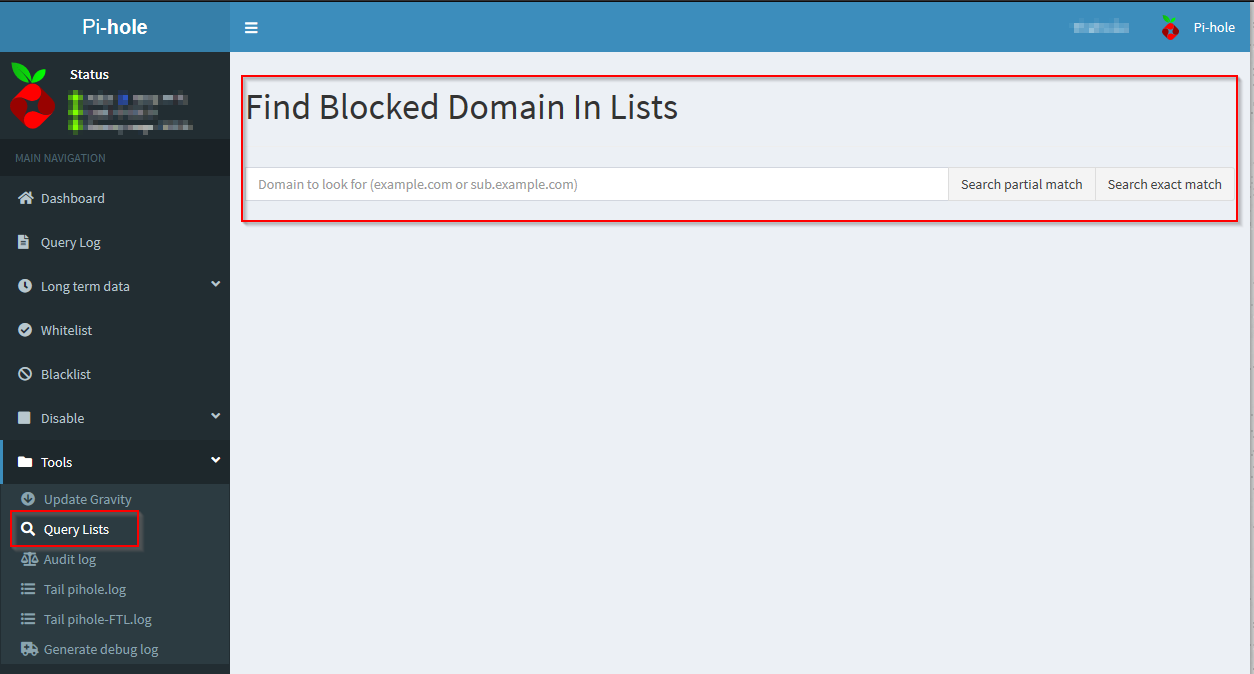
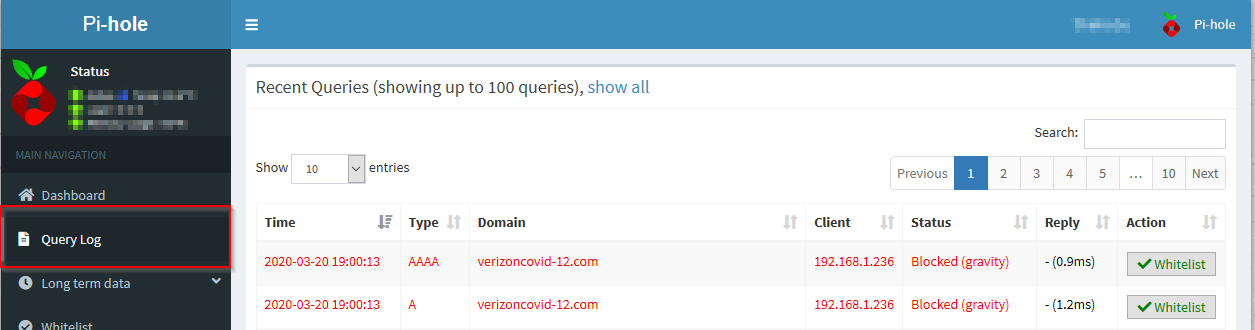
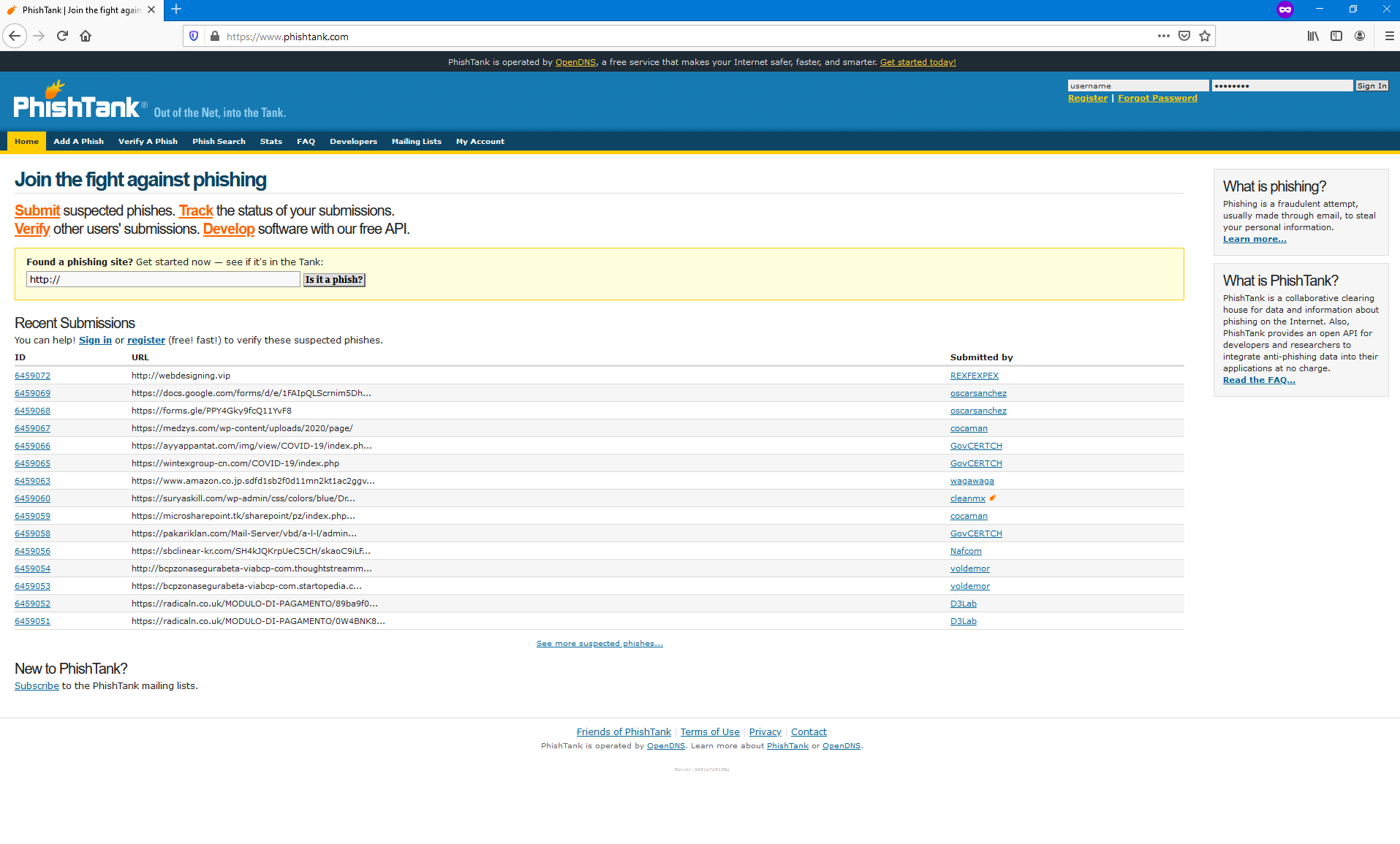
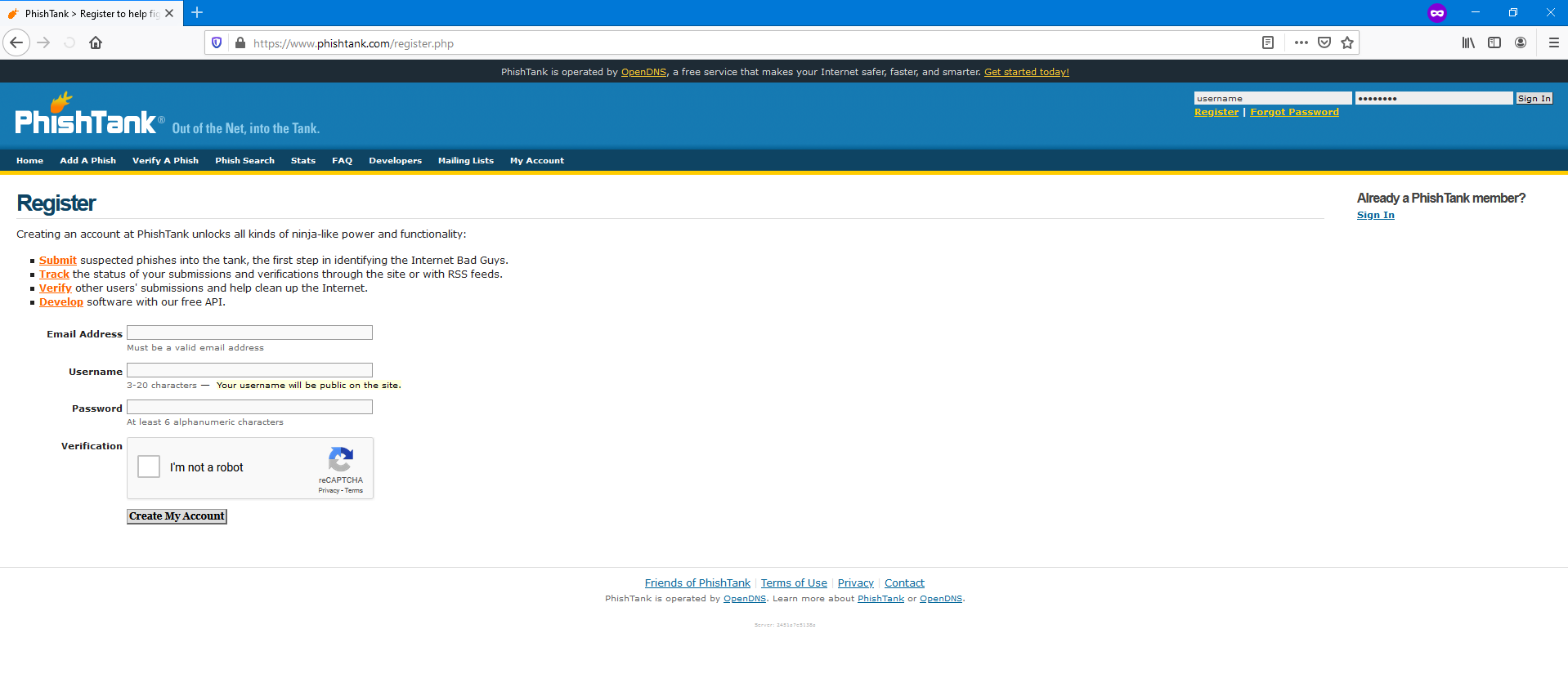
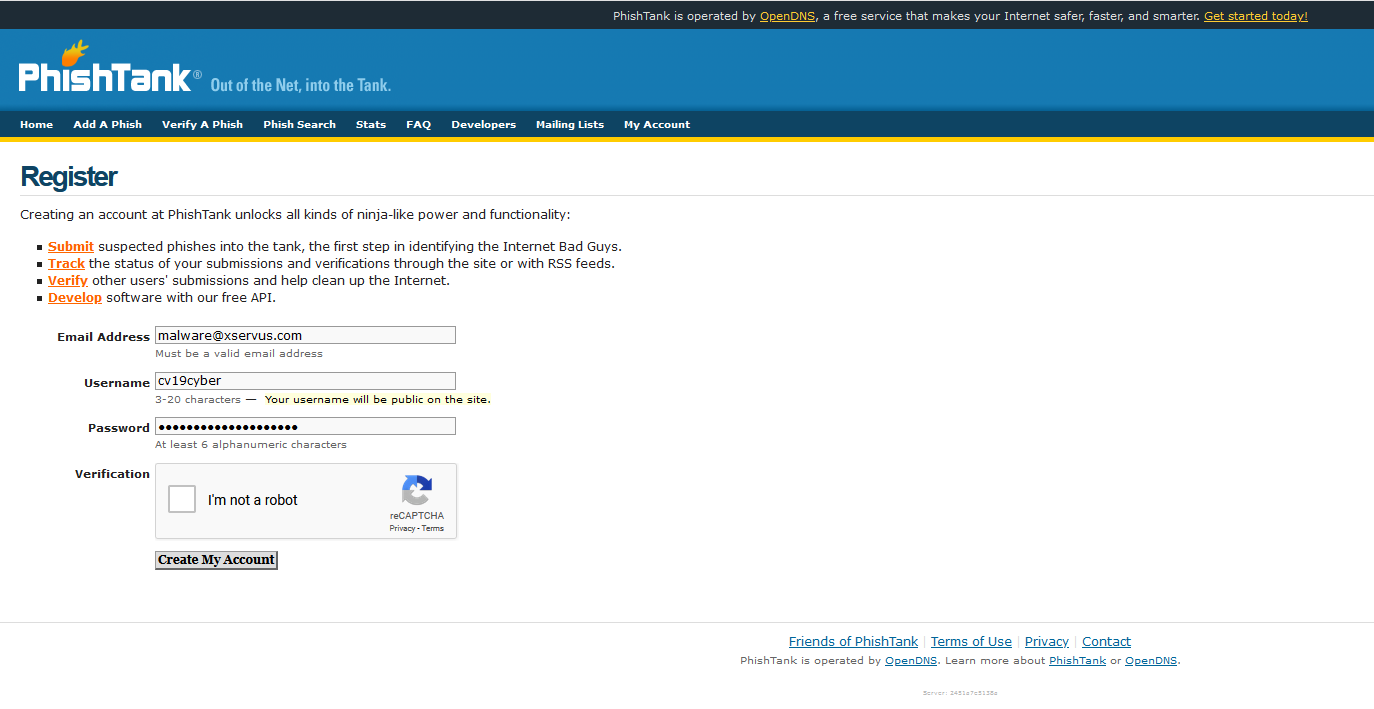
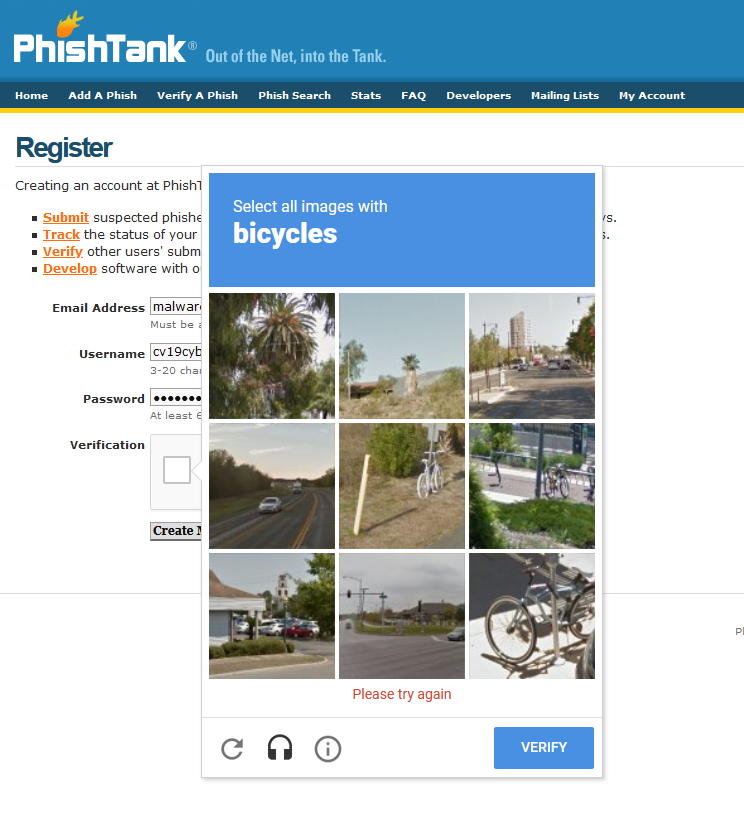
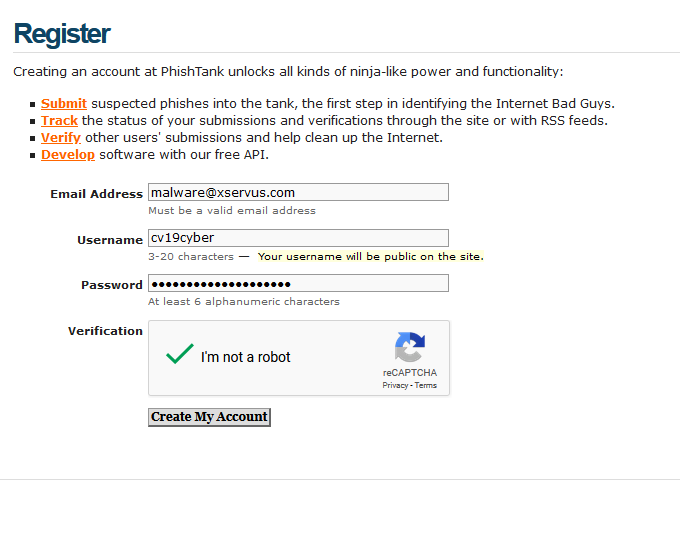
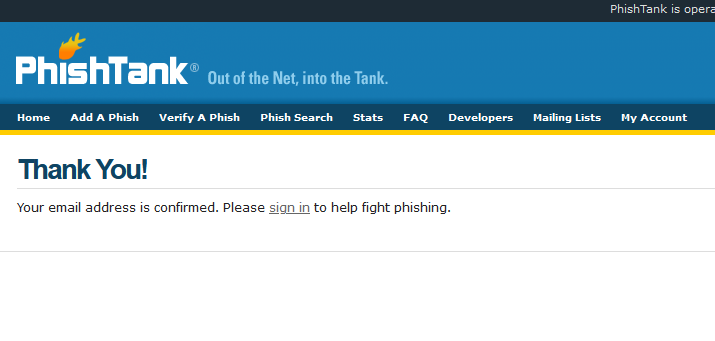
Phishing and Web Content Filtering
Our friends in the CTI league and Cyber Threat Coalition both publish independent block lists which can be leverage my mail hygiene and perimeter security solutions (such as Firewall and IPS/IDS systems)
https://github.com/COVID-19-CTI-LEAGUE/PUBLIC_RELEASE
https://blocklist.cyberthreatcoalition.org/vetted/
NCSC Weekly Threat Report
This report includes links to the phishing reporting service recently stood up by NCSC:
https://www.ncsc.gov.uk/information/report-suspicious-emails
https://www.ncsc.gov.uk/report/weekly-threat-report-3rd-july-2020