Introduction
Due to recent events related to COVID-19, some Health Centres in Europe have fallen victim to ransomware attacks. The first channel to spread ransomware is often phishing, so here are some suggestions to block web surfing to phishing sites if users have clicked on any emailed phishing links.
In my personal journey of learning about this technology, I installed some time ago Pi-hole Ad Blocking on my Raspberry Pi to avoid annoying commercials when surfing the net from home. Pi-hole can have more powerful applications as well, such as adding other types of blacklists to the Pi-hole – and a phishing site blacklist could be one of them.
The chain
The chain to follow to transform your Pi-hole into a DNS that blocks phishing links is pretty easy:
- Download and install Pi-hole; there are many guides on the Internet, depending on where you want to install it, here’s one for Raspberry.
- Add the phishing list to the adlist.list of your Pi-hole installation.
- Update your Gravity list.
- Report and vote for phishing sites.
- Check that Pi-hole blocks the right DNS queries.
As stated, the first step is pretty simple – yet it’s off topic here (ping the author if you are in trouble with the installation), so now to discuss directly the second point.
Add phishing list
I recently found a very good project that updates a phishing blacklist every 6 hours. This list could be implemented in your own Pi-hole installation to block phishing sites. It is called Phishing Army and it updates its lists directly from 3 sources:
Add Phishing Army blacklist to your Pi-hole
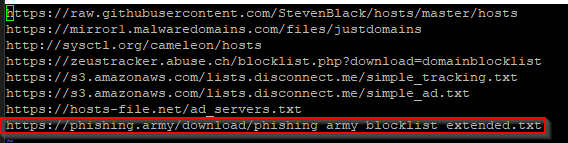
To add the Phishing Army blacklist to your Pi-hole simply add the list to the list file in the path /etc/pihole/adlist.list file in your Pi-hole installation. Just connect to the Pi-hole via ssh and type this command:
# vim /etc/pihole/adlists.list
Paste the link at the bottom of your list file, write and quit.
Update your Gravity list
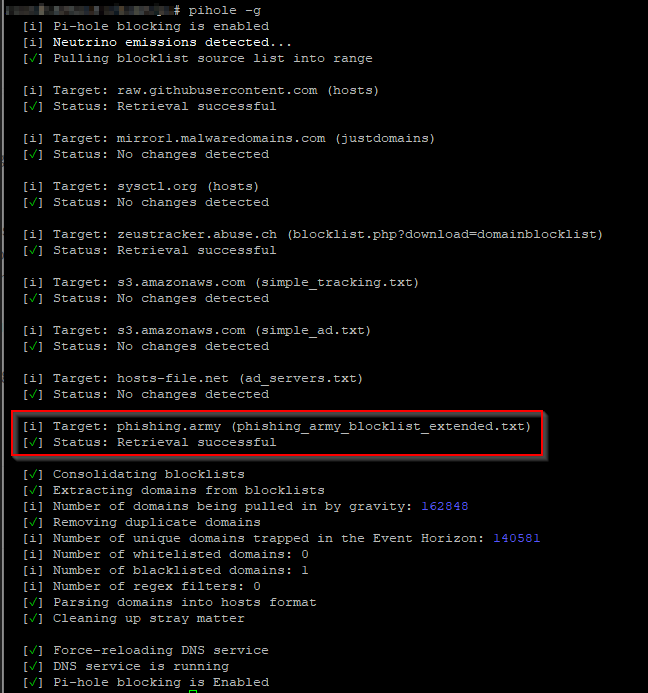
Now you have to update the Gravity black list by typing the command
# pihole -g
Report and vote for phishing sites
The first thing to do is to report and vote for phishing sites and the easiest way is to follow the instruction written on the amazing blog of the CyberV19 volunteers about using the voting system on Phishtank. When a Phishtank-submitted link reaches a good number of votes, it is marked as phishing. At this stage, it will then be put on the blacklist update of Phishing Army and automatically updated in the feed to your Pi-hole.
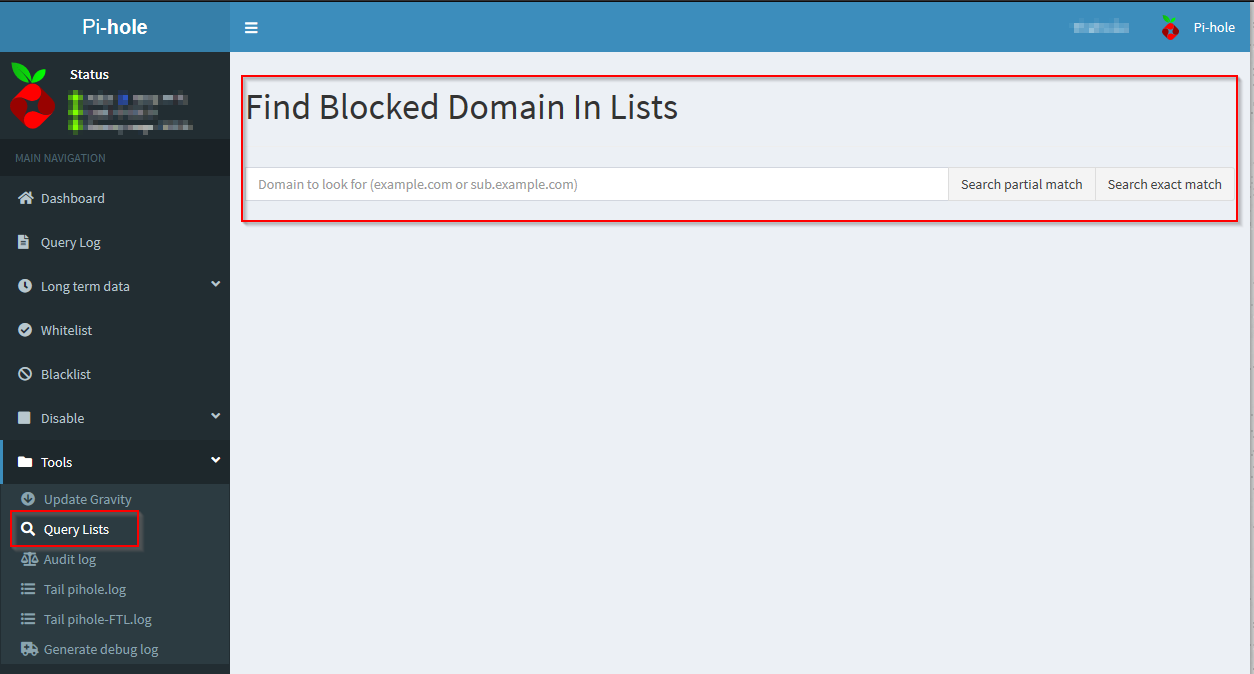
Checks
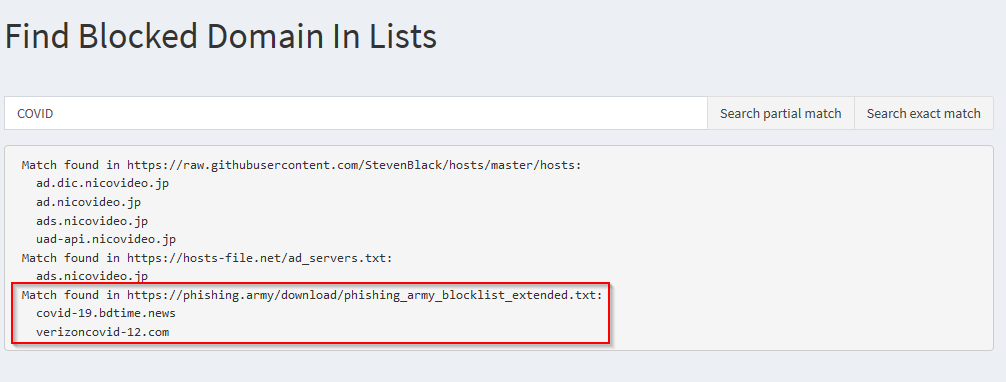
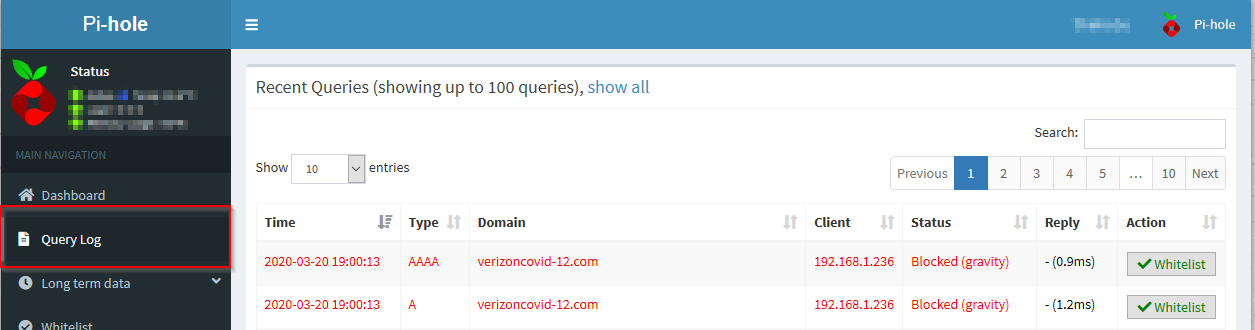
Now you can check if your Pi-hole is blocking malicious DNS requests. Search for a full or partial link in the Query Lists Search of the Pi-hole:
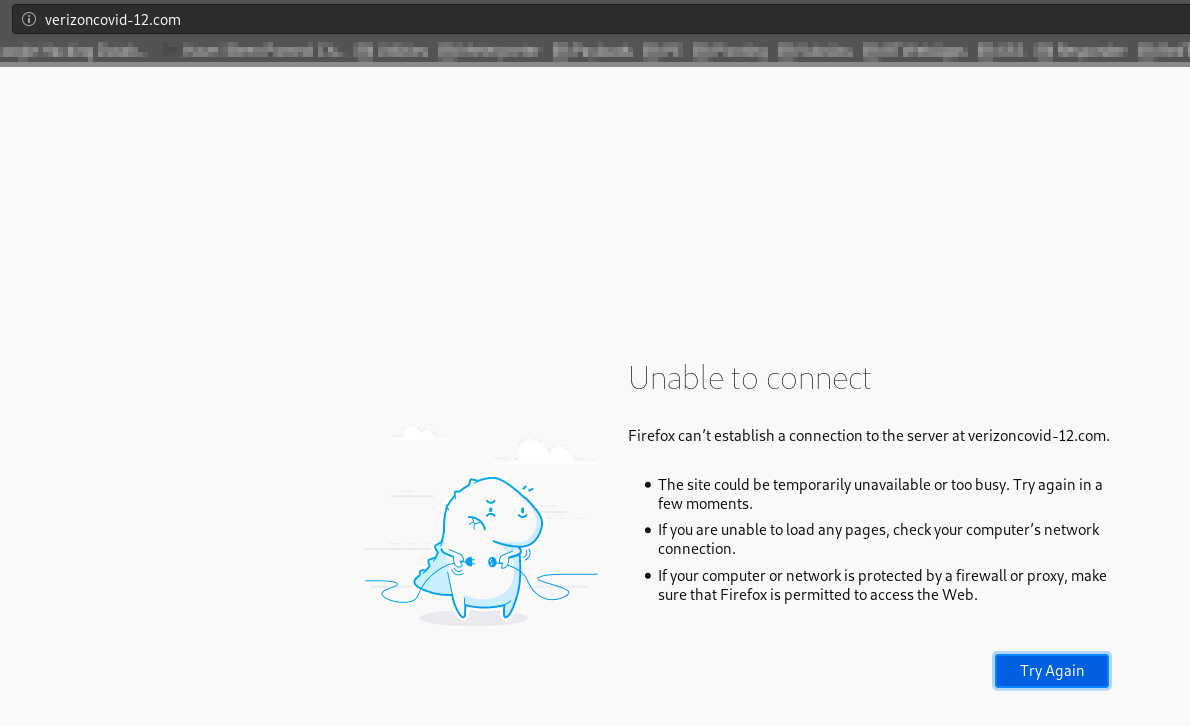
Try to surf to one of the links in the results and see the DNS query blocked by the Pi-hole:
Well done!
Conclusions
This is a home setup scenario. For a small company or test enterprise solutions, we would suggest installing Pi-hole in a docker container and configuring the Domain Controller to point to the Pi-hole as your primary DNS.
To reiterate, we recommend this setup for HOME use only. Hospitals and healthcare providers should use business class solutions for DNS services and protective DNS.
Thanks
Thanks to Luca Testoni for writing this blog and and contributing to CV19! This is a slightly modified version of the post on https://blackcloud.me/fight-phishing/